How to set up VNC server on Linux
Last updated on November 9, 2020 by Dan Nanni
Virtual Network Computing (VNC) allows you to share desktop environment on a local host with other remote users over network. To share desktop, a VNC server should be running on a local host, and remote users connect to the VNC server by using any VNC viewer client.
In this tutorial, I will explain how to configure VNC server on Linux. In this set up, I will use vino, VNC server software for the GNOME desktop environment.
Install vino on Linux
To install vino VNC server on Ubuntu, Debian or Linux Mint desktop:
$ sudo apt-get install vino
To install vino VNC server on Fedora, CentOS or RHEL desktop:
$ sudo yum install vino
Configure and Start vino VNC Server
After installation, you can start vino, and enable VNC server by entering vino-preferences command.
$ vino-preferences
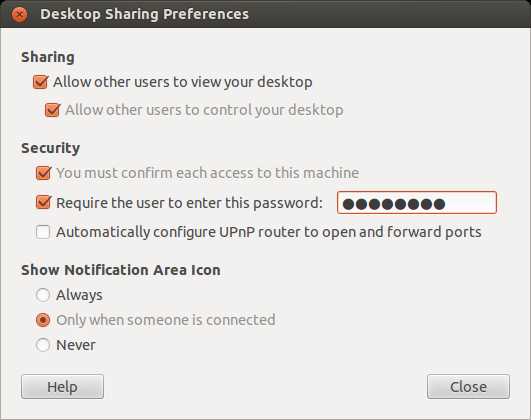
The above command will open up vino's desktop sharing preference window as shown below. On this window, click checkbox on Sharing to allow users to view and control your desktop. Optinally, set up VNC password. You can close the window after you are done with configuration.
The vino-preferences utility is then supposed to start vino VNC server automatically. If VNC server is not launched for whatever reason, you can start VNC server manually as follows.
$ /usr/lib/vino/vino-server &
On the latest Linux Mint Cinnamon desktop, vino-preferences is known to be missing. To enable and configure VNC server on Mint Cinnamon desktop, use dconf-editor instead, as described here.
You can check if vino is running by typing the following command.
$ sudo netstat -pl | grep vino
tcp 0 0 *:5900 *:* LISTEN 6646/vino-server tcp6 0 0 [::]:5900 [::]:* LISTEN 6646/vino-server tcp6 0 0 [::]:5800 [::]:* LISTEN 6646/vino-server
As shown above, vino-server is running on TCP port number 5800 and 5900. You can use any VNC client software to connect to the VNC server.
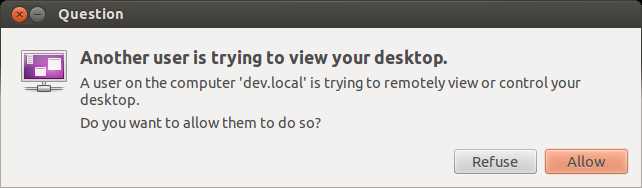
If VNC server is configured such that you must confirm each VNC access on your desktop, you will see the following pop up message every time a VNC connection request is received. Only when you allow VNC access, will VNC client be able to access your desktop.
Note that the Remote Frame Buffer (RFB) protocol used by VNC, by design, is not a secure protocol. Thus any sensitive information can leak from VNC traffic by traffic sniffing tools. To secure VNC traffic, it is recommended that you run VNC over an SSH tunnel.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

