What are popular packet sniffers on Linux
Last updated on November 16, 2020 by Dan Nanni
A packet sniffer tool captures live packets from networks, decodes them according to protocol specifications, and optionally takes actions according to the parsed packet contents (e.g., in case of intrusion detection/prevention systems). Packet sniffing tools are very useful when you diagnose networks or protect against security attacks over networks. The following list shows popular open-source packet sniffers that are available on Linux.
1. tcpdump
The most popular general-purpose packet analyzer. tcpdump uses libpcap library to capture packets on OSI layer 2 (e.g., Ethernet, PPP, and SLIP), and above. It also supports regular expressions for advanced packet filtering, and allows one to export and import packet dumps to and from a file.
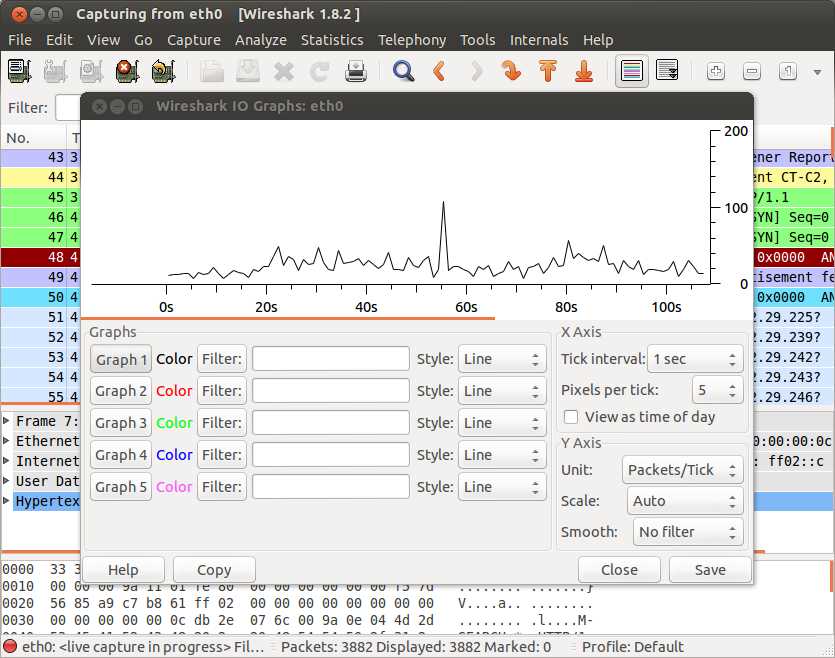
2. Wireshark
Formerly known as Ethereal, Wireshark is an open-source packet analyzer with graphical front end. Functionality-wise, Wireshark is quite similar to tcpdump, and is available on multiple platforms including Linux, BSD, and Mac OS X, and MS Windows. A CLI client called tshark comes with it.
3. dhcpdump
Snoops on DHCP request/response traffic captured by libpcap library, and displays the DHCP packets in human readable formats. dhcpdump is useful for DHCP debugging and troubleshooting.
4. p0f
A passive OS fingerprinting tool that identifies the operating systems of two end point hosts associated with an existing TCP connection. For accurate fingerprinting, p0f draws from various signatures including TCP/IP headers, TCP three-way handshake dynamics, contents of application-level payloads (e.g., HTTP request/response). Besides OS fingerprinting, p0f also detects the types of HTTP clients, network links (e.g., ethernet, DSL, modem), as well as NAT connection sharing, load-balancing setup, etc.
5. Snort
An open-source intrusion detection and prevention system that relies on real-time network sniffing and analysis. Snort conducts extensive protocol analysis and content matching to detect a variety of network attacks and hostile scans.
6. Kismet
A wireless network detector and intrusion detection system for 802.11 wireless links, supporting 802.11a, 802.11b, 802.11g, and 802.11n. It identifies wireless clients and their network association by passively collecting packets on wireless network card interfaces. Kismet also detects active wireless sniffing programs to alert wireless network attacks.
7. hcidump
A Bluetooth traffic sniffer which captures HCI packets associated with Bluetooth devices, and display Bluetooth related activities in human readable formats.
8. httpry
An open-source HTTP packet sniffing tool which captures live HTTP packets with libpcap library, and displays HTTP requests and responses in a human-readable format. It comes with a collection of parsing Perl scripts for mining various information from its standard output.
9. dsniff
A suite of CLI tools used for network auditing and penetration testing purposes. Supported functionality includes passwords from login sessions (dsniff), sniffing files from NSF traffic (filesnarf), email messages from SMTP/POP traffic (mailsnarf), URLs from web traffic (urlsnarf), etc.
10. ngrep
grep over network packets. Powered with libpcap library, it captures packets whose payload is matched with extended regular expressions or hexadecimal expressions.
11. ntopng
A full-blown web-based real-time network traffic monitoring system which provides flow/protocol/packet-level analysis of local network traffic. Long-term traffic history is archived in the database backend.
12. Wireless IDS
An open source intrusion detection tool for wireless networks. It sniffs communication between wireless devices and access points to detect any potential WEP/WPA/WPS attacking packets, or possible rogue access point.
13. mysql-sniffer
An open source MySQL sniffer tool which captures live packets sent to a MySQL server, and dumps MySQL queries in a human readable format.
14. bro
A powerful and flexible network monitoring and intrusion detection system. Analyzes live or recorded traffic to trigger events which are then handled by action policies.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

