How to configure WireGuard VPN client with NetworkManager GUI
Last updated on January 21, 2021 by Dan Nanni
WireGuard is an open-source VPN protocol implementation which is quickly gaining its popularity among VPN users due to its speed, ease-of-use and well-designed codebase. WireGuard kernel module is shipped with the mainline Linux kernel 5.6 or later, and its userland tools are already incorporated into the base repositories of all modern Linux distributions. If you are looking to set up a DIY VPN router on a public VPS under your control, there is really no reason not to try WireGuard.
Setting up a WireGuard VPN router does not require any expert knowledge on the underlying VPN protocol, nor involve learning cryptic configuration language or exploring huge configuration space. There are also various user-friendly frontends in the works that make client-side VPN configuration straightforward.
This tutorial focuses on setting up WireGuard VPN client by using a popular network management tool of choice: NetworkManager GUI.
Assumptions
In this tutorial, I assume that you have already set up a WireGuard VPN router somewhere (e.g., publicly accessible VPS). If you haven't done so, please refer to the following tutorial to set one up, and come back to this tutorial.
I also assume the following settings.
- WireGuard VPN server's WAN address:
192.168.122.104 - WireGuard VPN server's listening UDP port:
51820 - WireGuard VPN server's VPN address:
10.0.0.1/24 - WireGuard VPN client's VPN address:
10.0.0.2/24
Step One: Check Requirement
In order for you to be able to configure WireGuard VPN client with NetworkManager GUI, you need NetworkManager with version 1.26.2 or higher. So before proceeding, first check the version of your NetworkManager. Ubuntu 20.10, Fedora 33, and Arch Linux 2020.09.01 or later meet this requirement. So this tutorial is only applicable to one of those Linux desktop environments.
Step Two: Install WireGuard
Go ahead and install WireGuard with the default package manager.
For Ubuntu:
$ sudo apt install wireguard
For Fedora:
$ sudo dnf install wireguard-tools
For Arch Linux:
$ sudo pacman -S wireguard-tools
Step Three: Create a Cryptographic Key Pair
Next, create a public/private key pair for WireGuard VPN client. For this, let's first switch to the root. The rest of the steps in the tutorial will be performed as the root.
$ sudo -i
Use wg command to create a key pair and store them in /etc/wireguard.
# cd /etc/wireguard # umask 077 # wg genkey | tee /etc/wireguard/privatekey | wg pubkey | tee /etc/wireguard/publickey
Step Four: Add Client Public Key to WireGuard VPN Server
In order for WireGuard client to be able to talk to WireGuard VPN server, you need to explicitly add the client's public key to the VPN server. After all, WireGuard is a peer-to-peer VPN. So log in to the WireGuard VPN server host and run the following command.
# wg set wg0 peer <client-public-key> allowed-ips <client-VPN-address>
Note that in this example, the client's VPN IP address is 10.0.0.2.
Step Five: Create a Network Connection with NetworkManager's Connection Editor GUI
Next, run nm-connection-editor from the command line and add a new network connection for WireGuard VPN. Make sure to launch nm-connection-editor as the root as it needs to create a configuration file in /etc/NetworkManager/system-connections.
# nm-connection-editor
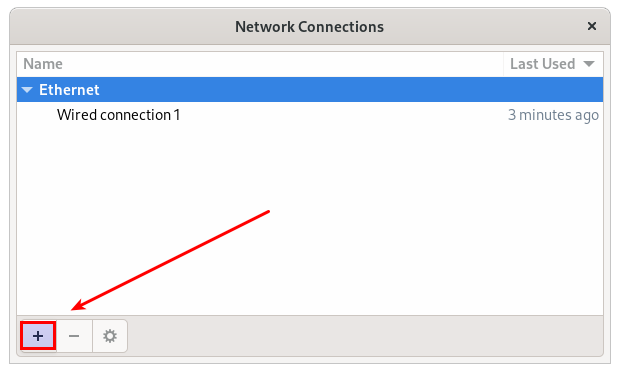
On Network Connections GUI, click on + button.
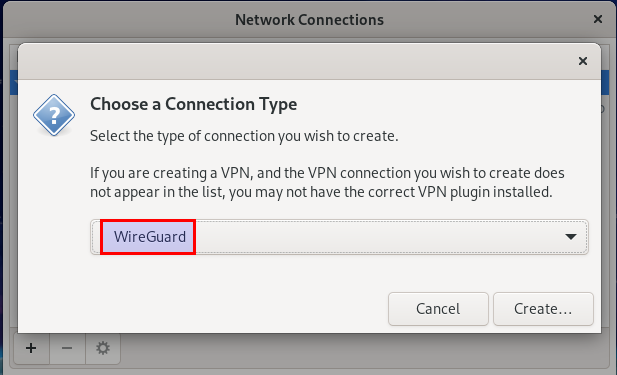
NetworkManager version 1.26.2 and higher, allows you to create a WireGuard-type connection. Thus go ahead and choose WireGuard as a connection type.
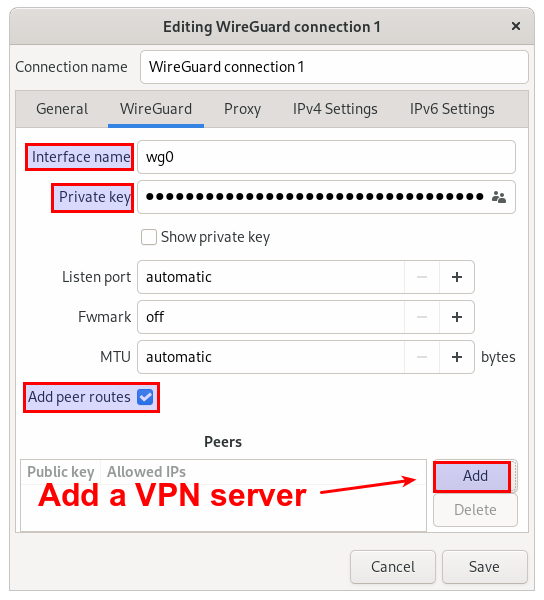
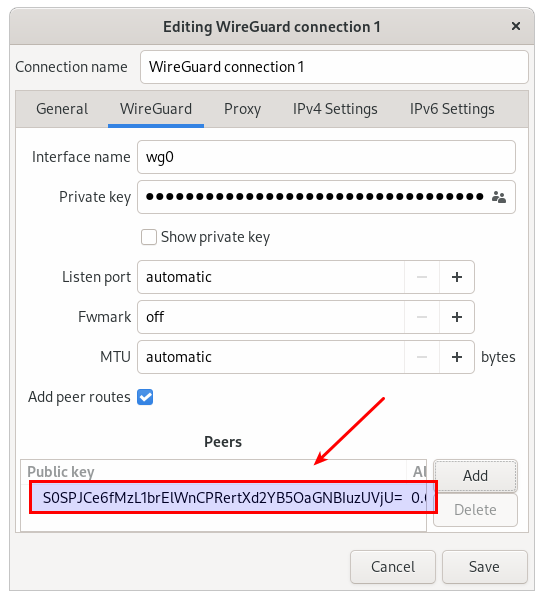
This will open up a connection editor window as follows. On WireGuard tab, set Interface name to wg0 and fill out Private key. The private key should come from the content of /etc/wireguard/privatekey you just created in Step 3. Then click on Add button at the bottom, which allows you to specify a WireGuard VPN server as a peer.
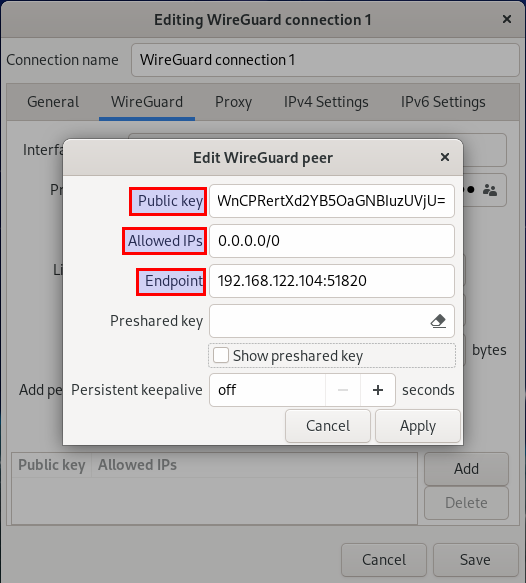
On WireGuard peer editor GUI, fill out Public key, Allowed IPs and Endpoint fields. The public key must comes from the WireGuard server. The endpoint consists of the WAN IP address of the VPN server and the UDP port that the server listens on. After filing them out, click on Apply button.
At this point you will see the VPN server added as a peer:
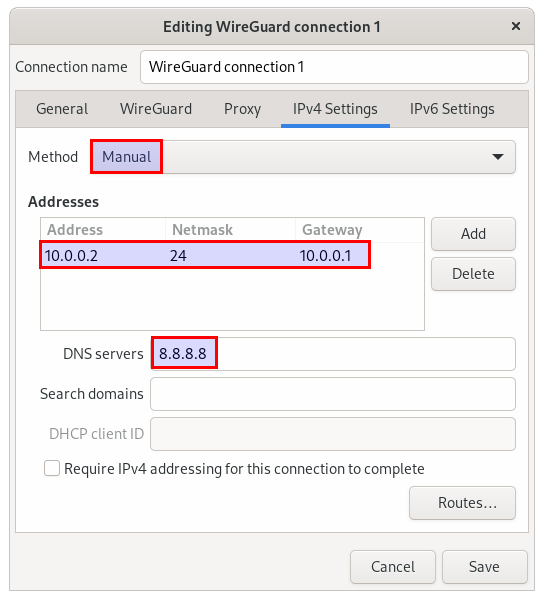
Next, go to IPv4 Settings tab, and configure a private VPN IP address to be assigned to WireGuard VPN client, which is 10.0.0.2/24. As a gateway, specify the VPN IP address of the WireGuard VPN server, which is 10.0.0.1/24. For DNS servers, you can pick any public DNS server (e.g., 8.8.8.8). Click on Save button.
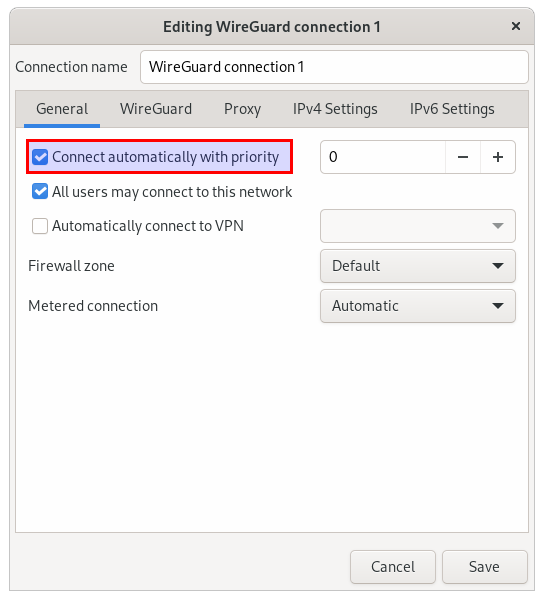
Now move to General tab, and turn on checkbox next to Connect automatically with priority. This will automatically activate this WireGuard connection and establish a VPN connection with the WireGuard VPN server. Click on Save button to finalize.
Step Six: Verify WireGuard VPN Connectivity
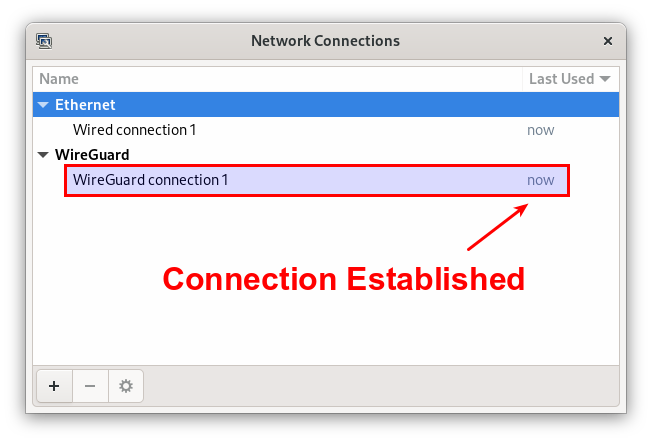
At this point, a WireGuard VPN connection should be up, and all outgoing traffic from client should be routed via the WireGuard VPN server.
To check WireGuard VPN connectivity on client-side, you can try pinging an external host (e.g., 8.8.8.8) from client's host. To verify that the ping traffic is routed via the WireGuard VPN server, use ip command.
# ping 8.8.8.8 # ip route get 8.8.8.8
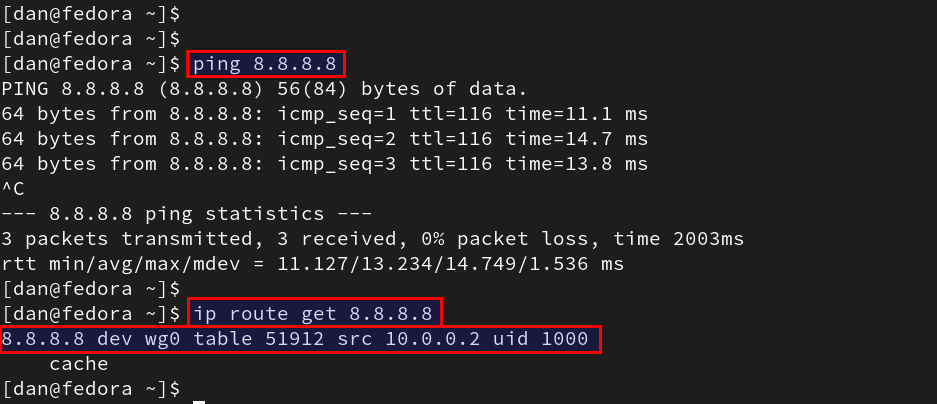
The ip route get <destination> command shows the route being used to reach the specified destination. The output of the command above confirms that traffic destined to 8.8.8.8 is routed via wg0 interface, not the WAN interface of the host.
Another way to verify the VPN connectivity is to run tcpdump on the WireGuard's virtual interface wg0 and check if the interface is seeing ICMP request and response traffic generated by the ping command.
# tcpdump -i wg0
Optional: Manage a WireGuard Connection from the Command Line
Once a WireGuard connection is successfully created with Network Manager GUI, you can manage the connection from the command line with nmcli as follows.
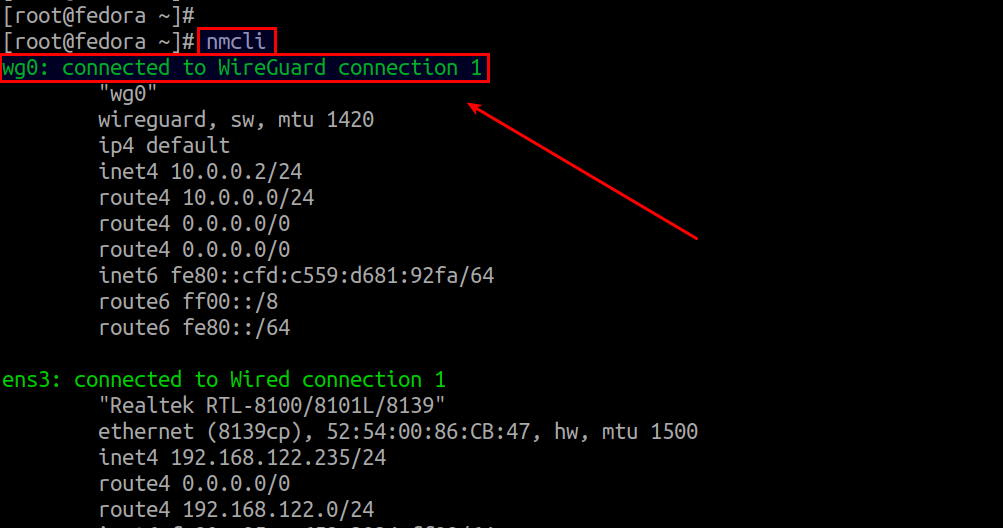
Simply run nmcli to see the status of VPN connection.
# nmcli
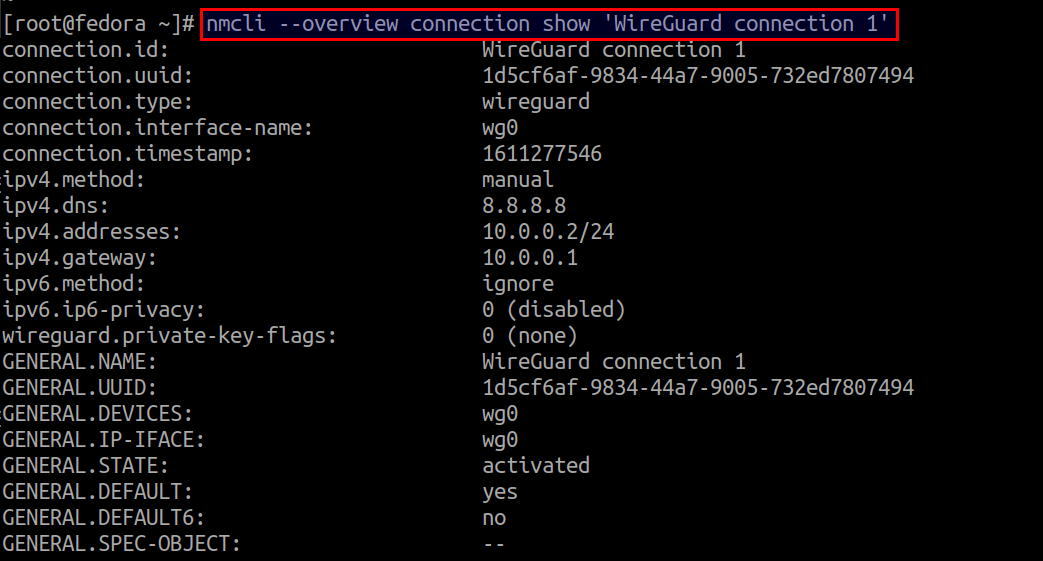
To see the detailed connection properties of WireGuard VPN:
# nmcli --overview connection show 'WireGuard connection 1'
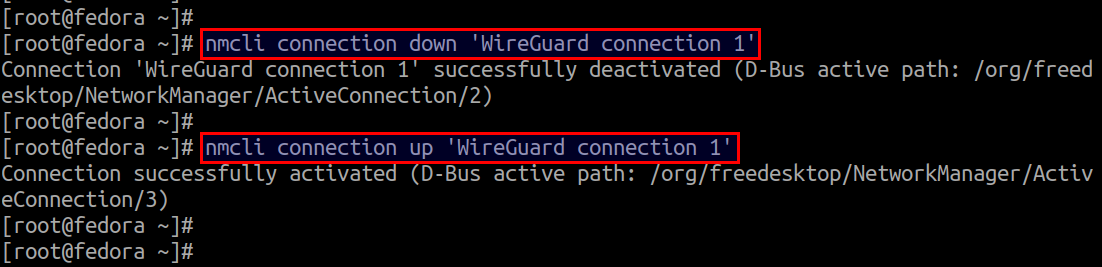
To start or stop WireGuard VPN:
# nmcli connection up 'WireGuard connection 1' # nmcli connection down 'WireGuard connection 1'
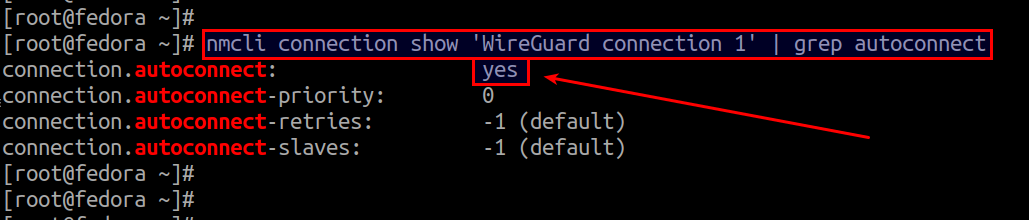
To check auto-start status of WireGuard VPN:
# nmcli connection show 'WireGuard connection 1' | grep autoconnect
To turn on/off auto-start of WireGuard VPN:
# nmcli connection modify 'WireGuard connection 1' connection.autoconnect yes # nmcli connection modify 'WireGuard connection 1' connection.autoconnect no
To delete the WireGuard VPN connection:
# nmcli connection delete 'WireGuard connection 1'
WireGuard VPN Troubleshooting
Symptom: You cannot ping the WireGuard VPN server's private IP address (10.0.0.1).
Solution 1: Check UDP port reachability
Make sure that the UDP listening port of the VPN server is accessible to the client. To check if that is the case, use the nc command.
# nc -zvu <VPN-server's-WAN-address> <UDP-port>
In our example:
# nc -zvu 192.168.122.104 51820
Connection to 192.168.122.240 51820 port [udp/*] succeeded!
If you cannot reach the UDP port, that's probably the server-side firewall blocking incoming traffic to the UDP port. Make sure to open up the port in the server-side firewall.
Solution 2: Check if client's public key is added to VPN server
Another possibility is that you forgot to add the client's public key to WireGuard VPN server. As described in Step 4 of this tutorial, use wg command to do that:
# wg set wg0 peerallowed-ips
Summary
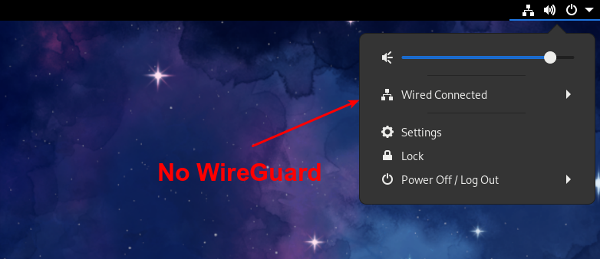
Once again this tutorial proved to you how easy it is to set up WireGuard VPN on modern Linux desktop. Although NetworkManager provides good enough support for WireGuard VPN, its full desktop integration (at least on GNOME desktop) is still not there. For example, as of NetworkManager 1.26.2, when WireGuard VPN is up, the network indicator does not show the status icon for WireGuard.
If you are using WireGuard VPN in a Linux desktop environment, share your experience in the comments.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

