How to set up a secure Apache webserver on Ubuntu
Last updated on September 13, 2020 by Dan Nanni
This tutorial assumes that you have a running Ubuntu Server, that networking has been set up, and that you have SSH access.
Apache HTTP server (Apache2) is the default web server used by many Linux installations. It is not the only one available, or the best for all circumstances, but it covers many usage scenarios. During the installation, you may be asked which webserver to reconfigure automatically. Answer apache2.
Install Apache2
Use the following command to install Apache2 and other libraries.
$ sudo apt-get -y install apt-get install apache2 apache2.2-common apache2-doc apache2-mpm-prefork apache2-utils libexpat1 ssl-cert libapache2-mod-php5 php5 php5-common php5-gd php5-cli php5-cgi libapache2-mod-fcgid apache2-suexec php-pear php-auth php5-mcrypt mcrypt libapache2-mod-suphp libopenssl-ruby libapache2-mod-ruby
Update TimeZone and Check Correct Time
To reduce confusion with shared or mirrored data, all servers ought to run as close to as in-sync as possible. Some cryptographic key management systems require accurate time. Lastly, for corporate servers, Sarbanes-Oxley and HIPAA Security Rules require accurate timestamping.
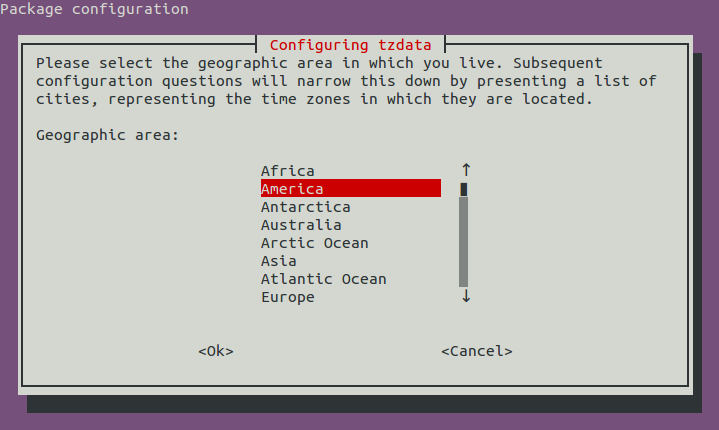
$ sudo apt-get -y install openntpd tzdata $ sudo dpkg-reconfigure tzdata $ sudo service openntpd restart
Disable AppArmor Conflicts
While AppArmor is a suite that does provide an additional layer of security, it is my opinion that custom profiles will need to be created for each system. That is something not covered in this tutorial. So for now, we are going to disable it to prevent conflicts with any default configurations.
$ sudo /etc/init.d/apparmor stop $ sudo update-rc.d -f apparmor remove $ sudo apt-get remove apparmor apparmor-utils
Note: disabling AppArmor is not recommended for a production web server. For those wanting to create a custom AppArmor profile, refer to the official documentation.
Protect Against DDoS Attacks
A DDoS attack is a distributed denial-of-service attack. An Apache module exists to stop such attacks, and it can be enabled as follows.
$ sudo apt-get -y install libapache2-mod-evasive $ sudo mkdir -p /var/log/apache2/evasive $ sudo chown -R www-data:root /var/log/apache2/evasive
Append the following to the bottom of mod-evasive.load.
$ sudo nano /etc/apache2/mods-available/mod-evasive.load
DOSHashTableSize 2048 DOSPageCount 20 # maximum number of requests for the same page DOSSiteCount 300 # total number of requests for any object by the same client IP on the same listener DOSPageInterval 1.0 # interval for the page count threshold DOSSiteInterval 1.0 # interval for the site count threshold DOSBlockingPeriod 10.0 # time that a client IP will be blocked for DOSLogDir “/var/log/apache2/evasive” DOSEmailNotify [email protected]
Stop Slowloris Attacks
An Apache modules also exist for Slowloris attacks, though the module name depends on which version of Ubuntu that you are using. For Ubuntu 12.10 or later:
$ sudo apt-get -y install libapache2-mod-qos
Then check configuration in qos.conf:
$ sudo nano /etc/apache2/mods-available/qos.conf
## QoS Settings
<IfModule mod_qos.c>
# handles connections from up to 100000 different IPs
QS_ClientEntries 100000
# will allow only 50 connections per IP
QS_SrvMaxConnPerIP 50
# maximum number of active TCP connections is limited to 256
MaxClients 256
# disables keep-alive when 70% of the TCP connections are occupied:
QS_SrvMaxConnClose 180
# minimum request/response speed (deny slow clients blocking the server,
# ie. slowloris keeping connections open without requesting anything):
QS_SrvMinDataRate 150 1200
# and limit request header and body (carefull, that limits uploads and
# post requests too):
# LimitRequestFields 30
# QS_LimitRequestBody 102400
</IfModule>
Note: If you are running a version of Ubuntu prior to 12.04, use the following instead.
$ sudo apt-get -y install libapache2-mod-antiloris
Check config in antiloris.conf.
$ sudo nano /etc/apache2/mods-available/antiloris.conf
<IfModule mod_antiloris.c>
# Maximum simultaneous connections in READ state per IP address
IPReadLimit 5
</IfModule>
Protect Against DNS Injection Attacks
Spamhaus is a module that uses DNSBL in order to block spam relay via web forms, preventing URL injection, block http DDoS attacks from bots and generally protecting the server from known bad IP addresses.
$ sudo apt-get -y install libapache2-mod-spamhaus $ sudo touch /etc/spamhaus.wl
Append the following configuration to apache2.conf
$ sudo nano /etc/apache2/apache2.conf
<IfModule mod_spamhaus.c> MS_METHODS POST,PUT,OPTIONS,CONNECT MS_WhiteList /etc/spamhaus.wl MS_CacheSize 256 </IfModule>
Restart Apache to load new modules.
$ sudo service apache2 restart
Or:
$ sudo systemctl restart apache2
Now the webserver has been installed and is up and running. Point your web browser at your domain for a default message that confirms you are working. As a final check, run the following to see if your server has any error message. If there are errors, you will want to Google them and address them now.
$ sudo tail -200 /var/log/syslog
Turn off Server Signature
Another source of potential security attacks is associated with web server signature, which reveals the version of Apache and PHP being deployed. The more detailed knowledge attackers have on your system, the better chance they have for exploiting potential vulnerabilities of the system. Follow this guideline to disable server signature on Apache.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

