How to set up a mail server in Ubuntu or Debian
Last updated on November 25, 2020 by Sarmed Rahman
This tutorial will discuss how to set up a working mail server in Ubuntu or Debian. As we know, the two major protocols used in a mail server are SMTP and POP/IMAP. In this tutorial, postfix will be used for SMTP, while dovecot will be used for POP/IMAP. Both are open source, stable and highly customizable.
Please note that securing a mail server is beyond the scope of this tutorial, and is covered in the following tutorials.
Prerequisites
Each domain should have a DNS server. It is recommended NOT to use a live domain for testing purposes. In this tutorial, a test domain example.tst will be used in a lab environment. A DNS server for this hypothetical domain should have the following records at the least.
Forward zone for example.tst:
IN MX 10 mail.example.tst. mail.example.tst. IN A 192.168.10.1
Reverse zone for example.tst:
192.168.10.1 IN PTR mail.example.tst.
While configuring a live mail server, these records can be changed based on system requirements.
Setting Hostname
First, the hostname of the mail server must be specified in /etc/hostname and /etc/hosts. The former should contain the hostname only.
root@mail:~# vim /etc/hostname
root@mail:~# vim /etc/hosts
## IP Fully Qualified Domain Name Hostname ## 192.168.10.1 mail.example.tst mail
Adding Users
Every Linux user, by default, has a mailbox automatically created. These users and mailboxes will be used as email accounts and their respective mailboxes. Creating a user is very easy.
root@mail:~# adduser sarmed
Install and Configure SMTP
Service Profile: postfix | |
| Configuration file directory | /etc/postfix/ |
| Script | /etc/init.d/postfix |
| Log file | /var/log/mail.log |
| Script | /etc/init.d/postfix |
| Port number | TCP/25 |
SMTP: Installing postfix
postfix is one of the most widely used SMTP servers because it is stable, lightweight, scalable, and highly customizable. Setting up postfix can be done using apt-get.
root@mail:~# apt-get install postfix
During installation, the type of email server and the domain name are specified.
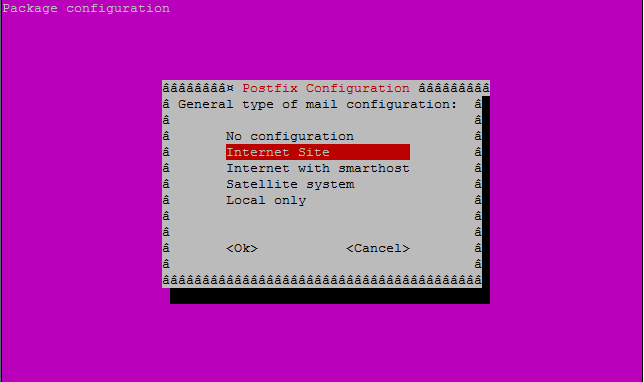
Since this mail server will send emails directly towards destination, Internet Site is used.
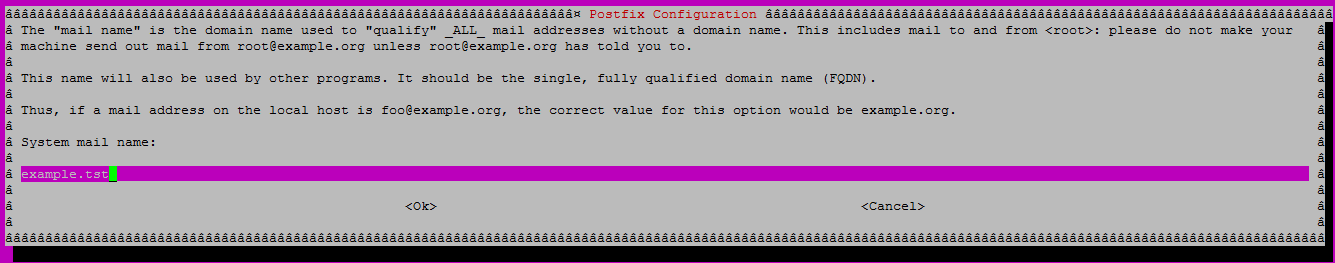
The domain name of the mail server is also set. This will cause all mails originating from this mail server to have @example.tst as the sender's domain.
The configuration files of postfix are stored in /etc/postfix. The following configuration files are important. Some of them may not be present and need to be created manually.
transport: Primarily used to define how a mail should be routed towards specific destination domains. Bypassing DNS queries can be a good example. In that case, one may need to send emails destined to domain XYZ.com directly to IP address X.Y.Y.X regardless of any DNS query results.access: Can be used for security purposes like blocking senders/recipients and their domains.aliases: Is used to define user aliases. For example, emails sent to userA should be received by userB and userC as well.main.cf: Is the configuration file forpostfix.
SMTP: Preparing Configuration Files
Time to prepare the configuration files. The transport and aliases files are not provided with the installation, and created manually.
root@mail:~# cd /etc/postfix root@mail:/etc/postfix# touch transport aliases
Configuring main.cf
main.cf is backed up and then modified. The following lines are added/modified in the configuration file. For more detailed info about the parameters, refer to the official README and configuration document.
root@mail:/etc/postfix# vim main.cf
## the name of the server ## myhostname = mail.example.tst ## alias definitions ## alias_maps = hash:/etc/postfix/aliases alias_database = hash:/etc/postfix/aliases ## transport definition ## transport_maps = hash:/etc/postfix/transport ## myorigin defines the domain name for emails originated from this server. In this case, all outgoing mail should have '@example.tst' as sender domain ## myorigin = example.tst ## mydestination parameter specifies what domains this machine will deliver locally, instead of forwarding to another machine. ## mydestination = mail.example.tst, localhost.example.tst, localhost, hash:/etc/postfix/transport ## the smarthost address. Not used in this tutorial and will be covered in the future## relayhost = ## the trusted sender networks. postfix will not forward mails originated from other subnets ## mynetworks = 127.0.0.0/8 [::ffff:127.0.0.0]/104 [::1]/128 192.168.10.0/24 ## mailbox size in bytes. 0 denotes no limit ## mailbox_size_limit = 0 ## postfix will listen on all available interfaces i.e. eth0, eth1, eth2 and so on ## inet_interfaces = all
Configuring transport
Mails destined to domain example.tst are defined to be delivered locally without any DNS queries.
root@mail:/etc/postfix# vim transport
example.tst local: .example.tst local:
root@mail:/etc/postfix# postmap transport
Configuring aliases
Assuming all mails sent to userA should be received by userB as well, the aliases file is modified as stated below.
root@mail:/etc/postfix# vim aliases
userA: userA, userB
root@mail:/etc/postfix# postalias aliases
Note: The syntax userA: userB specifies that the mail should be forwarded to userB only. userA will not receive a copy of the email.
SMTP: Initiating the Service
postfix can be started using the command.
root@mail:~# service postfix restart
The log file at /var/log/mail.log should provide useful information in case something fails. Whether or not the mail server is listening on TCP port 25 can also be verified using netstat.
root@mail:~# netstat -nat
tcp 0 0 0.0.0.0:25 0.0.0.0:* LISTEN
As it can be seen from the output, the server is listening on TCP port 25 for incoming connection requests.
Install and Configure POP/IMAP
Service Profile: dovecot | |
| Configuration file directory | /etc/dovecot |
| Script | /etc/init.d/dovecot |
| Log file | /var/log/mail.log |
| Script | /etc/init.d/dovecot |
| Port number | TCP: 110 (POP3), 143 (IMAP), 993 (IMAPS), 995 (POP3S) |
POP/IMAP: Installing dovecot
dovecot is without a doubt leading IMAP and POP server software used in the open source community. It is very easy to set up and configure dovecot. Once again, apt-get will be used to install dovecot.
root@mail:~# apt-get install dovecot-common dovecot-pop3d dovecot-imapd
Out of the box, dovecot can support POP3 and IMAP (plain text), as well as encrypted POP3S and IMAPS (secured). By default, dovecot will create and use a self-signed certificate for SSL encryption. Certificates can be manually created or imported later based on requirements. In this tutorial, a self-signed certificate generated by dovecot will be used.
POP/IMAP: Preparing Configuration Files
The following parameters are modified as needed.
root@mail:~# vim /etc/dovecot/conf.d/10-mail.conf
## the location of the mailbox is specified in 'mbox' format ## mail_location = mbox:~/mail:INBOX=/var/mail/%u ## dovecot is granted necessary permission to read/write user mailboxes ## mail_privileged_group = mail
That should be enough to start POP/IMAP service in the mail server.
POP/IMAP: Initiating the Service
Now that dovecot is installed and configured, it can be launched using the following command.
root@mail:~# service dovecot restart
Again, The log file (/var/log/mail.log) can provide important clues should something go wrong. Whether dovecot is running can also be verified using netstat.
root@mail:/etc/dovecot/conf.d# netstat -nat
ntcp 0 0 0 0.0.0.0:110 0.0.0.0:* LISTEN tcp 0 0 0 0.0.0.0:143 0.0.0.0:* LISTEN tcp 0 0 0 0.0.0.0:993 0.0.0.0:* LISTEN tcp 0 0 0 0.0.0.0:995 0.0.0.0:* LISTEN
Using the Mail Server with Mail User Agent (MUA)
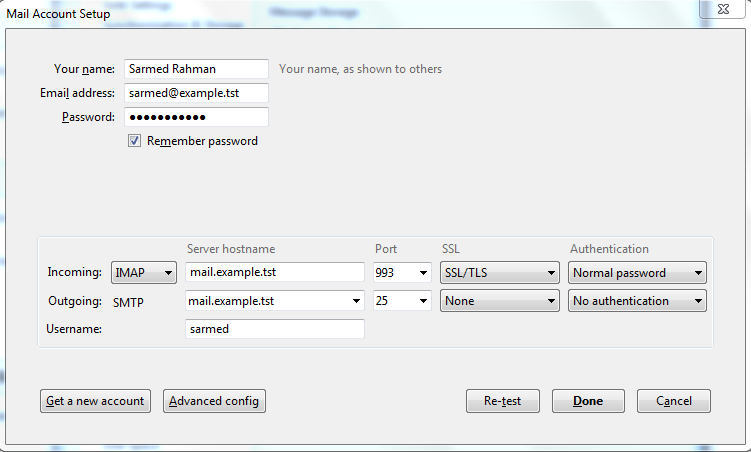
The mail server is now ready to be used. Email accounts can be configured using your favorite email client software in desktop, laptop, tablet or phone. Webmail can also be configured in the server, but setting up webmail will be covered in future tutorials. The following is a screenshot with necessary parameters in Mozilla Thunderbird.
Troubleshooting Mail Server
The log file /var/log/mail.log is your best friend. Any clue about why email is not working can be found here.
Make sure that the firewall is properly configured, and that the DNS server has proper entries.
To sum up, the demonstration in this tutorial is meant to run in a lab environment. A test DNS server with all necessary records can be deployed, and mails can be exchanged between users in the same server, i.e., same domain. To make things more interesting, multiple mail servers with different domains can be deployed to check how email communication works across domains, given that necessary DNS records are present.
Valid DNS records are needed for live mail servers. The settings of postfix and dovecot can be tuned based on needs.
Warning: For those who want to deploy live mail servers, or any mail server that has access to the Internet, make sure that your SMTP is secured. Attacks on SMTP can commonly originate from the Internet, as well as from malicious software within the LAN.
Hope this helps.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

